Different types of VPNs [Beginner Guide] 2023
L2TF/IPSec: this protocol generally uses AES(Advanced Encryption Standard) ciphers for…
- L2TP/IPSec: Layer 2 Tunneling Protocol and IP Security.
- PPTP: point-to-point tunneling protocol.
- OpenVPN: This is the most common and secure connection.
- IKEv2: Internet Key Exchange version 2.
- SSTP: Secure Socket Tunneling Protocol.
L2TF/IPSec: this protocol generally uses AES(Advanced Encryption Standard) ciphers for encryption. this protocol also offers high speed and high level of security for data packets as it supports 256-bit encryption. this protocol uses UDP on port 500.
L2TP(Layer 2 Tunnelling Protocol):
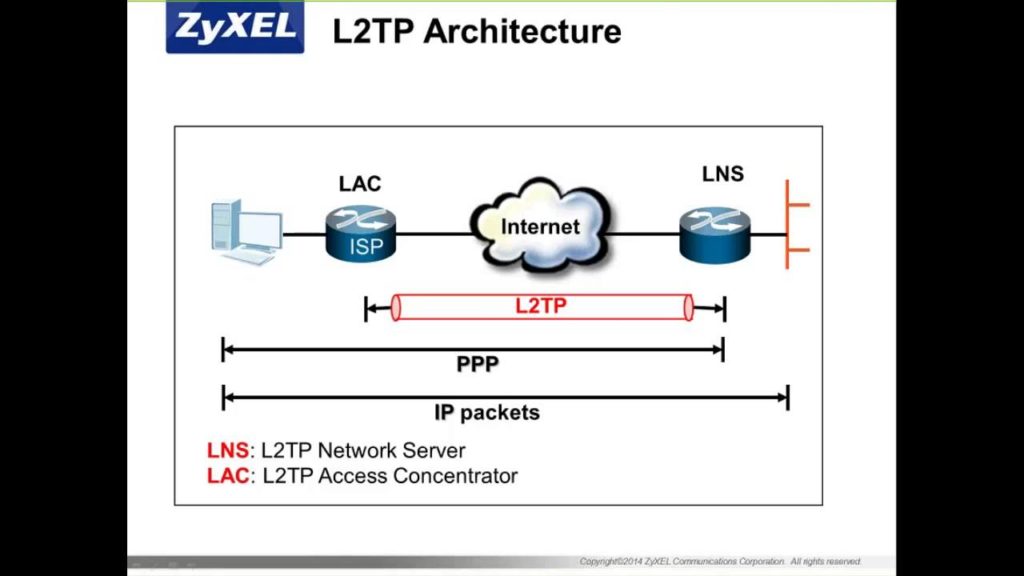
This protocol is used in combination with IPSec(Internet Protocol Security), due to the lack of confidentiality provided by L2TP. It is a combination of PPTP (Point-to-Point Tunnelling Protocol), developed by Microsoft and L2F (Layer 2 Forwarding), developed by Cisco.
L2TP operates on OSI layer 2. IPSec, AH, and ESP provide security services when L2TP is running over IPSec as L2TP does not provide encryption or privacy.
IPSec: stands for Internet Protocol Security
IPSec was developed by IETF(Internet Engineering Task Force) to ensure secure transfer of information across the internet.
One should use an algorithm and secret keys for the requested service as IPSec enables a system to select and negotiate the required protocols.
This provides data integrity, basic authentication, and encryption services to protect unauthorized viewing or modification of data.
It uses 2 security protocols for the required services.
- AH(Authentication Header)
- ESP(Encapsulated Security Payload)
1.AH(Authentication Header): provides source authentication and integrity of IP packets, but does not have encryption. These IP packets contain data, sequence numbers, and information which is used to verify the sender and ensures data integrity.
2.ESP(Encapsulated Security Payload): ESP uses symmetric encryption algorithms to provide data confidentiality. These algorithms need to be the same on both communicating parties.
PPTP(Point-to-Point Protocol):
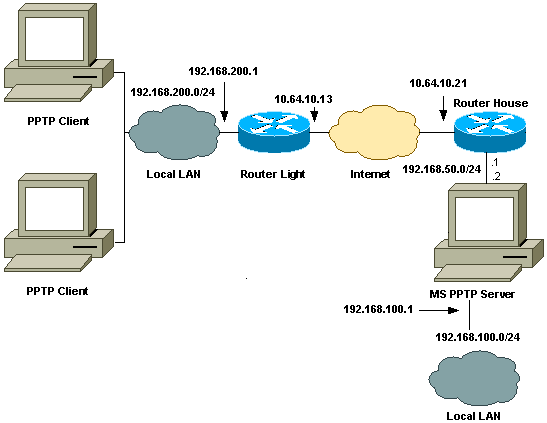
PPTP has been in use since 1996, developed by Microsoft. it is an OSI layer 2 protocol, built on the top of PPP(Point-to-Point Protocol) to encrypt the data between the connection.for each remote client, PPTP connects to the target network by creating a virtual network.
By using a modified version of GRE(Generic Routing Encapsulation), PPTP encapsulates PPP frames as tunneled data for transmission over the internet.
The generated GRE and PPP encapsulated data is then encapsulated with an IP header containing destination IP address for the client and server.
Upon receiving the PPTP tunneled data, to decrypt the PPP data, PPTP server processes and removes IP, GRE and PPP headers.
Tunneling Types Supported by PPTP
Voluntary Tunneling – This type of tunneling requires no ISP or bridge support as it is initiated by the client.
Compulsory Tunneling – Router and network access server support are necessary as this type of tunneling is initiated by the PPTP server.
make sure you only use it for accessing or streaming geo-blocked content. although it is very fast, it is not secure at all and can be exploited by cybercriminals with malicious attacks. also, this VPN protocol can be blocked easily by the firewall.
OpenVPN:
OpenVPN is an open-source Vpn. this protocol is extremely popular for its enhanced security and is used for site-to-site and point-to-point connections.it uses a custom security protocol based on SSL & TLS(Transport Layer Protocol).
OpenVPN uses 256 bit OpenSSL encryption. this VPN might use the AES, Camellia, 3DES, CAST-128, or Blowfish ciphers, to strengthen the security of the connection.
OpenVPN uses UDP(User Datagram Protocol) and TCP(Transmission Control Protocol) transmission protocols.
Speeds tend to drop quite often with OpenVPN due to its strong encryption. make sure you use OpenVPN over UDP instead of TCP to get faster speeds.
OpenVPN is one of the safest VPN protocols you can use to enjoy a private, surveillance and hacker-free online experience.
IKEv2(Internet Key Exchange Version 2):
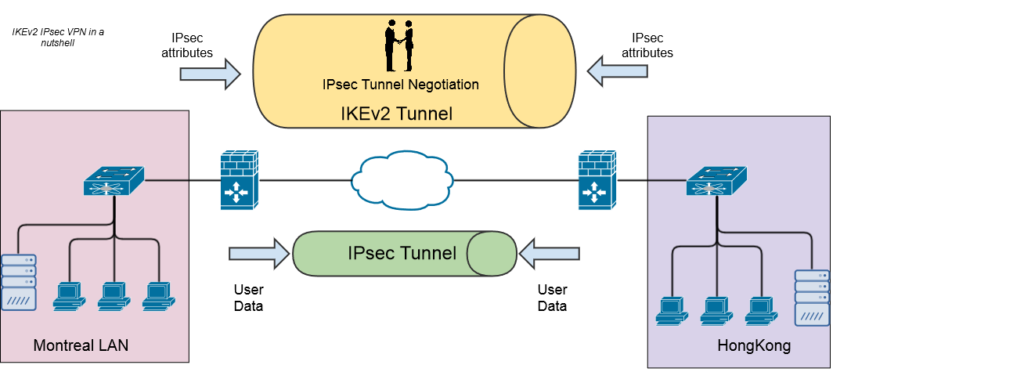
The IKEv2 protocol was released in 2005, developed by Microsoft and cisco together.IKEv2 is the latest version of the IKE(Internet Key Exchange).
(IKE) protocol security is high as it uses high-end cipher like AES, 3DES, CAMELLIA and chacha 20 and supports 256-bit encryption which makes it safe to use.
IKEv2, like many other VPN protocols, establishes a secure tunnel between the VPN client and the VPN server. It first authenticates both the client and the server, and then agrees on which encryption methods to be used.
IKEv2 handles security attributes between two network entities (the client and the server). It does that by generating the same symmetric encryption key for both entities which is then used to encrypt and decrypt all the data that travels through the VPN tunnel.
SSTP (Secure Socket Tunneling Protocol):
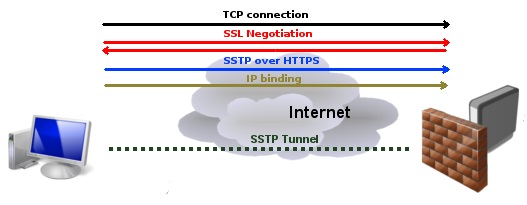
SSTP is a VPN protocol that was developed by Microsoft.this VPN protocol encrypts online communications between a client and a server.SSTP cannot be blocked easily by firewalls since it uses port 443. this protocol has limited cross-platform compatibilities like Windows, Android, Linux, and routers.
SSTP uses 256-bit encryption and AES encryption cipher and offers a decent level of security. this VPN encryption is considered relatively safe to use when browsing the internet. it uses SSL 3.0 and encapsulates data packets over HTTPS.
However, it is vulnerable to the “TCP meltdown” problem, as an issue might occur with the TCP connection which takes place over the TCP transmission protocol that is created within the VPN tunnel.
A conflict between the two connections occurs when there is a TCP connection within the TCP connection which causes connectivity issues.
Also, not many users trust it fully because it is owned by Microsoft, which is well known to collaborate with the NSA.
we hope this guide is helpful, if you have any further doubts or queries regarding VPN Types please let us know in the comment box.


![How to fix [pii_pn_33004351a30a92ea] error?](https://techyguide.net/wp-content/uploads/2020/08/techyguide-feature-image-28-300x169.jpg)

![How to fix [pii_email_aef67573025b785e8ee2] error?](https://techyguide.net/wp-content/uploads/2020/08/techyguide-feature-image-27-300x169.jpg)

